Our Services
Consultations and help
Our IT staff is prepared to provided all the needed information for you to be able to choose the most suitable software solution for your business. Free consultations are provided on demand. If our clients prefer we can arrange personal visits to help with an occurring problem or need.
Free Trials. Without limitations
Our preference is that clients would be fully informed about the solution they are getting. We provide 30 day trials for every software program we offer.
Our solutions to help your business
Get protected from DDoS attacks
Your website can be safe
How can we help?
Every business risks being hacked or damaged by cyberattack. DDoS Guard is a cyber security platform, that works as a gate between the internet and your infrastructure, to block hacker activities.
We’ve created a complete solution: a privacy and security service that guards all your web infrastructure. DDoS Guard covers all common threats in real-time and provides tools to improve security.
It is very important for businesses to stay online at all times and to keep their data safe. That’s why DDoS Guard is a smart choice, providing a high ROI. Take care of your business, while we take care of your cyber security!
DDoS Guard is easy to install: you don’t need to buy hardware, or get into long and expensive projects to integrate it with your website or apps. The installation takes less than 5 minutes.
Malicious bots can detect web application vulnerabilities and communicate the information back to hackers.
Instantly detected
Hackers attempting to steal personal and private information from your website, web application or cloud and trying to infect your clients.
Automatically detached
Malicious bots or hackers may try to corrupt your systems and damage your business, resulting in lost income and damaged reputation.
Distinguish between good and bad traffic and filter malicious bots
How it works?
There are two criteria for an amplification attack:
1. A query can be sent with a spoofed source address (e.g., via a protocol like ICMP or UDP that does not require a handshake); and
2. The response to the query is significantly larger than the query itself. As DNS is a core, ubiquitous internet platform that meets these criteria, it has become the largest source of amplification attacks.
Do you provide SSL certificates?
In addition we provide free SSL certificates issued automatically with the help of the LetsEncrypt service, as well as the possibility to upload your custom certificate (if you want to use wildcard or EV certificate). This will help you to ensure that the connection from NISPS to visitors is encrypted and safe.
Order DDoS Guard Now
Every Internet application can benefit from using DDoS Guard.
Pick a plan that fits your needs.
Preparing for the General Data Protection Regulation
GDPR will affect your data protection policy
How can we help?
In May 2018, a new EU-wide data protection regulation comes into force. If it affects you, you will need to start to thinking about compliance now. The General Data Protection Regulation (GDPR) will affect every organization in Europe that handles personal data of any kind. It will also affect any company that does business in the EU. The rules are complex and fines for non-compliance are significant (up to €20 million).
But you are in the right place to learn more!
Why encryption is an important element in data security?
Encryption is the process of encoding information in a way that prevents unauthorized parties from being able to read it.
Key length and encryption strength
Encryption strength is most commonly equated to key length (bits) and the encryption algorithm used. The simplest way to defeat encryption is to try all the possible keys. This is known as a brute-force attack, but longer keys have made this approach ineffective.
How does it work?
Encryption is applied, most commonly, in two different ways:
Encrypted storage – often referred to as ‘data at rest’ – is most commonly used to encrypt an entire disk, drive or device.
This type of encryption becomes effective only once the system is stopped, the drive ejected or the encryption key blocked.
Encrypted content – also referred to as granular encryption – means, typically, encrypting files or text at the application level.
The most common example is email encryption, where the message format must remain intact for the email client application to be able to handle it, but the text body of the email is encrypted along with any attachments.
Strong two-factor authentication
Single-tap authentication for extra data protection – ESET Secure Authentication. ESET Secure Authentication helps you secure your data – in a hassle-free way. By complementing your normal authentication with a second factor, it effectively reduces the risk of data breaches caused by weak or leaked passwords.
Data loss prevention
Safetica protects you from expensive data leaks and unnecessary personnel costs.
Data loss prevention
Safetica keeps key data inside your company. Employees can’t take important information to a competitor or start their own businesses
Social engineering
Safetica can detect socially engineered attacks and blackmail attempts at the initial stages, preventing them from damaging your company.
Misdirected files
Safetica prevents important files from getting into the wrong hands, either inside or outside the company, and warns management of potential dangers.
Lost laptops & thumbdrives
Important data is protected by Safetica even if lost on the road. The whole disc or selected files remain encrypted and unreadable by the thief.
Visit ESET website for more information: https://encryption.eset.com/lt/
Data leak prevention
Strictest personal data protection
regulation comes into force in the EU
How Can we help?
Your data is your most important asset. Keep it safe with Safetica.
Safetica prevents data leaks, so that your customer data doesn’t land in someone else’s hands.
Safetica is a cost-effective, easy-to-use Data Loss Prevention (DLP) solution. It performs security audits, prevents sensitive data from leaving your company and sheds light on what is going on in your organization. Safetica can be installed in a matter of hours – it secures your information quickly and easily.
With Safetica you’ll learn:
- What data leaked out of your company
- Who manipulated confidential data without authorization
- How much time do your employees spend playing games
- What documents were printed unnecessarily
- Which software licenses are not being utilized
Safetica gives you:
- Analysis of your company’s internal security
- Real-time notifications in case of incident
- Monthly overviews, emailed straight to your inbox
- WebSafetica Online for internal audits
- Safetica offline console for admins
Cyber security training for employees
Your security is only as strong as your weakest link
How can we help?
With user-friendly terminology and tips, this flexible, on demand Cybersecurity Awareness Training covers everything employees need to know to keep your business’ data and devices.
Training overview
- Threats Overview: Malware, phishing & social engineering
- Password Policies: Best practices; 2FA and how to use it
- Web Protection: What to look for; what to avoid
- Email Protection: What to look for; what to avoid
- Preventive Measures: Best practices for security at home and business
Also have you considered doing a penetration test?
91% of data breaches originate from social engineering activities. Social engineering is the most effective form of cybercrime. Cybercriminals are aware of the vulnerability of your employees and exploit this to gain access to your corporate data.
Social Engineering Assessment of ESET examines the security awareness of your employees using a customized phishing campaign. In consultation with you, the campaign is set up by an ESET Cyber Security Engineer. The results and statistics may be presented on location or delivered to you by means of an analysis report.
ESET Intelligence Labs perform penetration testing and code review for all platforms of mobile applications and have created a dedicated testing environment fully equipped for testing Android based application. We also provide a “Black Box” type test, when the clients system is penetrated without any previous knowledge about the system.
Our penetration testing labs use the most advanced technologies to test mobile applications and analyze the security stature of the application. We have dedicated environments for testing both iOS and Android applications. These dedicated environments allow us to test and analyze the application optimally, on its real environment /device.
During the testing, we simulate a multitude of attacks, both general application attacks and mobile dedicated attacks. The testing simulates a real hacker and what he can do to penetrate the application and retrieve confidential data.
Backup and restore data
End-to-end data protection
and business continuity
How can we help?
Total data protection with Xopero. Comprehensive protection of all business environment Protect your entire business environment, no matter where your data is stored. Xopero secures your endpoints, mobile devices, servers, mailboxes, databases, virtual machines and more.
Recovering your data is not enough – business environments increasingly rely on specialised programs and applications. Xopero ensures your business continuity by comprehensively protecting your entire system.
An advanced backup service for demanding business needs. Provides protection for unlimited computers, databases and both physical and virtual environments. A business-class solution, designed for SMBs and large corporations, which expands the functionality of your QNAP NAS, turning it into a private cloud backup.
Enterprise network vulnerability tests
Want to verify the security posture of your network, web, mobile and desktop applications?
How can we help?
91% of data breaches originate from social engineering activities. Social engineering is the most effective form of cybercrime. Cybercriminals are aware of the vulnerability of your employees and exploit this to gain access to your corporate data.
The Social Engineering Assessment of ESET examines the security awareness of your employees using a customized phishing campaign. In consultation with you, the campaign is set up by an ESET Cyber Security Engineer. The results and statistics may be presented on location or delivered to you by means of an analysis report.
ESET Intelligence Labs perform penetration testing and code review for all platforms of mobile applications and have created a dedicated testing environment fully equipped for testing Android based application. We also provide a “Black Box” type test, when the clients system is penetrated without any previous knowledge about the system.
Our penetration testing labs use the most advanced technologies to test mobile applications and analyze the security stature of the application. We have dedicated environments for testing both iOS and Android applications. These dedicated environments allow us to test and analyze the application optimally, on its real environment /device.
During the testing, we simulate a multitude of attacks, both general application attacks and mobile dedicated attacks. The testing simulates a real hacker and what he can do to penetrate the application and retrieve confidential data.
Network Traffic Analysis
Improve Your Cyber Security Posture and Network Visibility
How can we help?
We use advanced methods of artificial intelligence, machine learning and data mining to help organizations make their IT operations more secure and reliable. GREYCORTEX MENDEL employs advanced machine learning, unique detection algorithms and several additional traditional detection methods for detection of both known and unknown threats.
GREYCORTEX MENDEL differs from other Network Performance Monitoring, Diagnostics and Application Monitoring solutions in several crucial aspects: its application awareness, identity awareness and a flow-based monitoring engine that processes more features (six times more features than NetFlow, for example).
GREYCORTEX MENDEL is designed for Advanced Security Network Monitoring of critical infrastructure and other high-demand environments. The advantages of MENDEL technology including artificial intelligence, risk assessment, an intuitive web user interface and robust filtering will help you accomplish much more in less time.
GREYCORTEX MENDEL incorporates many cutting edge technologies with several ground breaking ones to be implemented soon.
Our technology is designed using a combination of our extensive experience, customer feedback on competing products and Brno University of Technology team research, which has succeeded repeatedly at NIST challenges.
Latest data reports tailored to your business needs
See and understand your data
How can we help?
Bussines intelligence is focused on one thing – helping people see and understand data. Organizations everywhere, from non-profits to global enterprises, and across all industries and departments, are empowering their people with data.
With Business intelligence service they are finding opportunities in their business that they have never seen before.
We provide a full service, working with top – industry leading software solutions.
We save your time by handling all the installation, licensing and management needs leaving you with a ready to work environment. Learn more about how organizations like yours are using our platform to drive their business forward.
Data encryption
Encryption is an important element in data security
How can we help?
Encryption is the process of encoding information in a way that prevents unauthorized parties from being able to read it.
Key length and encryption strength
Encryption strength is most commonly equated to key length (bits) and the encryption algorithm used. The simplest way to defeat encryption is to try all the possible keys. This is known as a brute-force attack, but longer keys have made this approach ineffective.
How does it work?
Encryption is applied, most commonly, in two different ways:
Encrypted storage – often referred to as ‘data at rest’ – is most commonly used to encrypt an entire disk, drive or device.
This type of encryption becomes effective only once the system is stopped, the drive ejected or the encryption key blocked.
Encrypted content – also referred to as granular encryption – means, typically, encrypting files or text at the application level.
The most common example is email encryption, where the message format must remain intact for the email client application to be able to handle it, but the text body of the email is encrypted along with any attachments.
Strong two-factor authentication
Single-tap authentication for extra data protection – ESET Secure Authentication. ESET Secure Authentication helps you secure your data – in a hassle-free way. By complementing your normal authentication with a second factor, it effectively reduces the risk of data breaches caused by weak or leaked passwords.
Data loss prevention
Safetica protects you from expensive data leaks and unnecessary personnel costs.
Data loss prevention
Safetica keeps key data inside your company. Employees can’t take important information to a competitor or start their own businesses
Social engineering
Safetica can detect socially engineered attacks and blackmail attempts at the initial stages, preventing them from damaging your company.
Misdirected files
Safetica prevents important files from getting into the wrong hands, either inside or outside the company, and warns management of potential dangers.
Lost laptops & thumbdrives
Important data is protected by Safetica even if lost on the road. The whole disc or selected files remain encrypted and unreadable by the thief.
GDPR will affect your data protection policy
How can we help?
In May 2018, a new EU-wide data protection regulation comes into force. If it affects you, you will need to start to thinking about compliance now. The General Data Protection Regulation (GDPR) will affect every organization in Europe that handles personal data of any kind. It will also affect any company that does business in the EU. The rules are complex and fines for non-compliance are significant (up to €20 million).
But you are in the right place to learn more!
Antivirus and Cyber security
Our only objective is to keep your system secure
How can we help?
ESET Endpoint protection – Multi-layered technology far beyond basic antivirus. Today’s malware, being dynamic and often targeted, requires a multi-layered approach based on proactive and smart technologies. As far back as 30 years ago, ESET started to incorporate proactive technologies into its scanning engine and gradually implemented different layers of protection to strike at different stages of the cyber kill chain.
The more multi-layered your security, the fewer incidents you’ll need to resolve:
Network Attack Protection
protects against vulnerabilities for which a patch has not yet been released or deployed.
Botnet Protection
protects against infiltration by botnet malware – preventing spam and network attacks launched from the endpoint.
Exploit Blocker
new detection technology that strengthens protection against targeted attacks and previously unknown exploits – i.e. zero-day attacks.
World-class antivirus and antispyware
eliminates all types of threats, including viruses, rootkits, worms and spyware with optional Cloud Malware Protection System.
ESET Remote Administrator
Single point of network security management
ESET protects all of the most-used operating systems with the same level of functionality, leaving no potential entry point to your network unprotected.
ESET’s powerful security management console gives you real-time information on the security state of your network, endpoints and mobile devices, including security and administration functionality that protects you against threats.
- ESET Remote Administrator runs on both Windows and Linux systems
- Immediate response to possible incidents
- Handle tens of thousands of clients while maintaining high-speed operation
- Built-in Mobile Device Management component
Team building tools
New era of employee engagement
How can we help?
Smart and intuitive social intranet solution made for effective communication, empowerment, acknowledgement and social networking of your company employees.
It encourages more interactions, more social activities, more fun. Focus on what’s important and create the atmosphere of respect and acknowledgment. Make your team building experience and everyday task with this innovative company intranet software.
Network management
Gathering and monitoring information in your network – integrated IT management and security
How can we help?
Our flagship product, Axence nVision®, responds to the key needs of IT administrators and security officers in the scope of network and user monitoring, hardware and software inventory, remote technical support, data protection against leakage and analyzing productivity at work. It enables the management to optimize the operating costs of any IT infrastructure, regardless of its size.
6 MODULES CREATES COMPLETE SOLUTION FOR YOUR NEEDS
NETWORK
When you need to monitor the devices which are present and operating in your network and when you want to be informed in advance about any potential failures in the network.
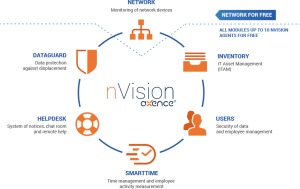
INVENTORY
When you want to have a full list of installed software close at hand, track app licenses, store and manage all IT assets in one place.
USERS
When you want to prevent problems with the security of company data, and care about the efficient management of user access and authorizations.
HELPDESK
When you need to manage notices of employees and respond to them easily, and you want to quickly provide them with remote help.
DATAGUARD
When you want to increase the security level in your organization by protecting your data against leaks and network infection from pen drives, and when you want to define security policies for the connected storage media.
SMARTTIME
When you care about the identification of employee and team activities which consume the most time, and want to optimize the effectiveness of work in key areas.
If you have any questions or want to make an inquiry about a proposal – leave us a message here